Introduction
Cloud adoption has transformed how businesses operate, and Microsoft Azure stands at the forefront of this shift. Organizations rely on Azure for scalability, flexibility, and performance, but moving to the cloud does not eliminate security risks. In fact, it introduces new challenges that traditional security approaches often fail to address.
This is where Azure penetration testing becomes essential. It allows organizations to simulate real-world cyberattacks and uncover vulnerabilities before malicious actors exploit them. With increasing data breaches and cloud misconfigurations, proactive testing is no longer optional—it is a critical component of modern cybersecurity strategy.
What is Azure Penetration Testing?
Azure penetration testing is a controlled security assessment process designed to identify weaknesses in cloud infrastructure, applications, and configurations hosted on Azure. Unlike automated vulnerability scans, penetration testing involves ethical hackers who actively attempt to exploit vulnerabilities in a safe and authorized manner.
The purpose is not just to detect issues but to understand how far an attacker could go if those vulnerabilities were exploited. This includes analyzing identity systems, storage configurations, APIs, and network security controls. Because Azure environments are highly dynamic, penetration testing provides a realistic picture of your actual security posture.
Why Azure Penetration Testing is Important
Many organizations assume that cloud providers handle all aspects of security, but Azure follows a shared responsibility model. While Microsoft secures the underlying infrastructure, customers are responsible for securing their own data, applications, and configurations. This gap often leads to serious vulnerabilities.
Azure penetration testing helps uncover hidden risks such as exposed storage accounts, weak authentication systems, and overly permissive access controls. It also plays a key role in meeting compliance requirements like ISO 27001, SOC 2, and HIPAA. Beyond compliance, it provides real-world insights into how attackers think and operate, enabling businesses to strengthen their defenses effectively.
Scope of Azure Penetration Testing
The scope of Azure penetration testing can vary depending on business requirements, but it generally includes multiple layers of the cloud environment. Testing often begins with infrastructure components such as virtual machines, networking configurations, and load balancers. From there, attention shifts to applications, including web apps, APIs, and serverless functions.
Identity and access management is another critical area, especially within Azure Active Directory, where misconfigured roles can lead to privilege escalation. Storage systems are also evaluated to ensure sensitive data is not publicly accessible. Finally, network security is analyzed to identify open ports, weak firewall rules, and insecure connections that could expose the system to external threats.
Azure Penetration Testing Methodology
A structured methodology ensures that Azure penetration testing delivers accurate and actionable results. The process typically begins with planning and scoping, where the testing boundaries, assets, and permissions are clearly defined. This step is crucial to ensure compliance with Microsoft’s policies and to avoid unintended disruptions.
Once the scope is defined, the next phase focuses on reconnaissance. During this stage, testers gather information about the Azure environment, identify exposed services, and map the attack surface. This information forms the foundation for identifying potential entry points.
The testing process then moves into vulnerability discovery, where both automated tools and manual techniques are used to detect security weaknesses. However, the most critical phase is exploitation, where testers attempt to use these vulnerabilities to gain unauthorized access or escalate privileges. This step reveals the real-world impact of each vulnerability.
Post-exploitation activities help determine how far an attacker could move within the system, whether sensitive data can be accessed, and how easily control can be expanded across the environment. Finally, a detailed report is prepared, outlining vulnerabilities, their severity, and practical remediation steps.
Common Vulnerabilities in Azure Environments
Azure environments are powerful but complex, and this complexity often leads to misconfigurations. One of the most common issues is publicly exposed storage accounts, where sensitive data becomes accessible without authentication. Identity-related weaknesses are also frequent, especially when users or applications have more permissions than necessary.
Insecure APIs represent another major risk, particularly when authentication or input validation is not properly implemented. Network-level vulnerabilities, such as open ports and weak firewall rules, can allow attackers to gain initial access. Additionally, the absence of proper monitoring and logging makes it difficult to detect suspicious activities in real time, increasing the risk of prolonged attacks.
Tools Used in Azure Penetration Testing
Azure penetration testing combines automated tools with manual expertise to achieve the best results. Security professionals often rely on tools that can scan for vulnerabilities, analyze configurations, and simulate attack scenarios. However, tools alone are not sufficient.
The real value comes from human-driven testing, where ethical hackers think like attackers and uncover complex vulnerabilities that automated systems might miss. This combination of automation and manual testing ensures a comprehensive assessment of the Azure environment.
Microsoft Rules for Azure Penetration Testing
Microsoft allows penetration testing on Azure resources without prior approval, provided that organizations follow specific guidelines. These rules are designed to ensure that testing activities do not disrupt services or impact other users.
Testing your own applications and services is permitted, but activities such as denial-of-service attacks are strictly prohibited. Organizations must ensure that their testing remains within authorized boundaries and complies with Microsoft’s policies. Following these rules not only ensures safety but also maintains trust within the cloud ecosystem.
Best Practices for Azure Penetration Testing
To maximize the effectiveness of Azure penetration testing, organizations should adopt a proactive and continuous approach. Testing should not be treated as a one-time activity but as an ongoing process that evolves with the environment.
Implementing the principle of least privilege helps reduce the attack surface by ensuring that users and applications only have the access they truly need. Strengthening identity systems with multi-factor authentication adds an additional layer of protection. At the same time, enabling detailed logging and monitoring ensures that any suspicious activity can be detected and addressed quickly.
Combining automated tools with manual expertise provides deeper insights and more accurate results. Regular testing after updates or infrastructure changes ensures that new vulnerabilities are identified before they can be exploited.
When Should You Perform Azure Penetration Testing?
Azure penetration testing should be conducted at critical stages of the business lifecycle. It is particularly important after migrating to the cloud, as new environments often contain misconfigurations. Testing before launching applications ensures that vulnerabilities are addressed before they reach users.
Major infrastructure changes, such as updates or integrations, can introduce new risks, making testing essential during these transitions. Regular assessments, at least once a year, help maintain a strong security posture and ensure ongoing protection against evolving threats.
Benefits of Azure Penetration Testing
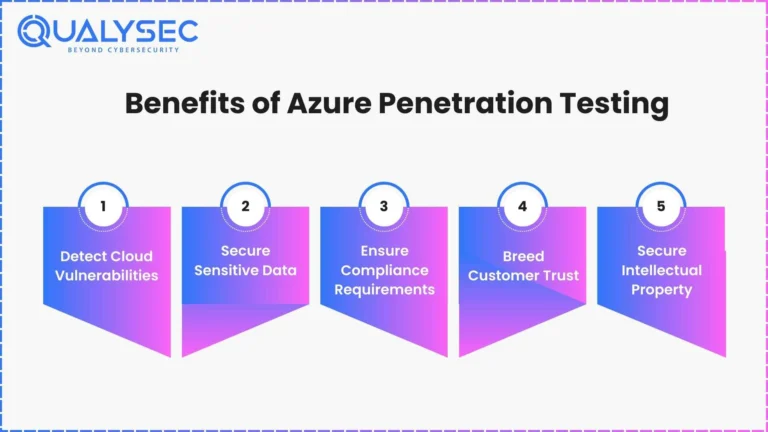
Azure penetration testing provides a clear understanding of an organization’s security strengths and weaknesses. It enables early detection of vulnerabilities, reducing the risk of data breaches and financial losses. By identifying and addressing issues proactively, businesses can improve their overall security posture and build trust with customers.
It also supports compliance efforts by demonstrating a commitment to security and risk management. In addition, penetration testing enhances incident response capabilities by revealing how attackers might operate within the environment.
Challenges in Azure Penetration Testing
Despite its importance, Azure penetration testing can be complex due to the dynamic nature of cloud environments. Resources are constantly being created, modified, and removed, making it difficult to maintain visibility.
The shared responsibility model can also create confusion about which aspects of security are handled by Microsoft and which are the responsibility of the customer. Without proper understanding and expertise, organizations may overlook critical vulnerabilities.
Conclusion
Azure penetration testing is a vital component of cloud security in today’s digital landscape. As organizations continue to rely on Azure for critical operations, the need for proactive security measures becomes increasingly important.
By identifying vulnerabilities, simulating real-world attacks, and implementing effective remediation strategies, businesses can protect their data, maintain compliance, and stay ahead of cyber threats. Investing in regular Azure penetration testing is not just a security measure—it is a strategic decision that ensures long-term resilience and success in the cloud.